Phishing is no longer just advancing in its techniques. It is accelerating at an unprecedented pace, making it tough for users to stay updated. Cybercriminals today are also advancing in their approaches that go beyond poorly written emails or obvious scams. Instead, they are using AI scam tools to create hyper-realistic messages, mimicking writing styles, cloning voices, and automating attacks at a greater scale.
The outcome? Even technically adept users are struggling to differentiate between reality and scams.
Since the digital age is the new norm, it is widely adopted across the world of banking, social platforms, and even work. So it is important to understand what phishing is, how it works, and its types, to stay aware of any malicious attacks.
Why Phishing Attacks Are More Dangerous Than Ever
Phishing is no longer operating alone and can be identified with ease. It is now present in a highly interdependent digital ecosystem where attackers constantly develop strategies to exploit it. Nowadays, AI scam detection tools like Jortty are assisting in detecting suspicious behavior and anomalies.
Advanced technologies are also being exploited by cybercriminals to circumvent these defences. This back-and-forth has contributed to phishing attacks being more persistent and adaptive and has complicated their control by users and organisations.
Key Factors Driving Modern Phishing Risks
Today’s phishing landscape is shaped by a combination of technological advancements and human vulnerabilities. Several key factors have made these attacks significantly harder to detect and prevent:

- Highly personalized communication that uses real names, roles, and context to appear legitimate.
- Authentic brand impersonation through cloned logos, email templates, and domain spoofing.
- Multi-channel attack delivery spanning email, SMS, voice calls, and social media.
- AI-powered content generation that produces flawless, convincing messages at scale.
Phishing is no longer just one method but a combined method of evolving tactics, and knowing about types of phishing attacks is central to remaining protected.
A Closer Look at Modern Phishing Techniques
Now, let’s dive into the most prevalent phishing attacks found in the modern day and discuss how each one of those works in practice.
Email Phishing (Deceptive Phishing)
This common attack involves bulk mailing that pretends to be a reputable brand to defraud recipients by clicking on malicious links or downloading infected files. This is usually done through the use of a sense of urgency, fear, or curiosity to take action now.
How it works
- The email is a call to action (e.g., “Your account has been suspended).
- It contains a malicious link or attachment.
- Victims are lured to spoof sites that steal or install malware.
Red flags
- Generic greetings (Dear Customer).
- Questionable sender email addresses.
- Threatening or desperate wording.
Being more suspicious of unsolicited emails and checking the sources can play a significant role in not becoming a victim of any deceptive phishing attack.
Spear Phishing
An extremely specific form of phishing where hackers tailor messages with personal information, making communication look valid and significant. This dramatically raises the probability of victims believing the message and engaging in damaging behavior.
How it works
- Before commencing an attack, the attacker investigates the victim.
- Emails look very real and pertinent.
- Frequently employed to deliver access to business systems or confidential information.
Why it’s dangerous
Due to the personal and legitimate nature, even cautious users can fall into its trap.
Whaling (CEO Fraud)
Whaling targets high-level executives, who receive carefully crafted messages written from the perspective of people they trust. This is to facilitate the signing of huge financial transactions or reveal secretive business information that usually creates huge financial and credibility losses.
How it works
- Leveraging the roles of executives or partners, attackers pose as them.
- They demand important financial operations or information.
- Involves counterfeit invoices or payment instructions.
Impact
Such attacks may result in extensive financial damages and data losses.
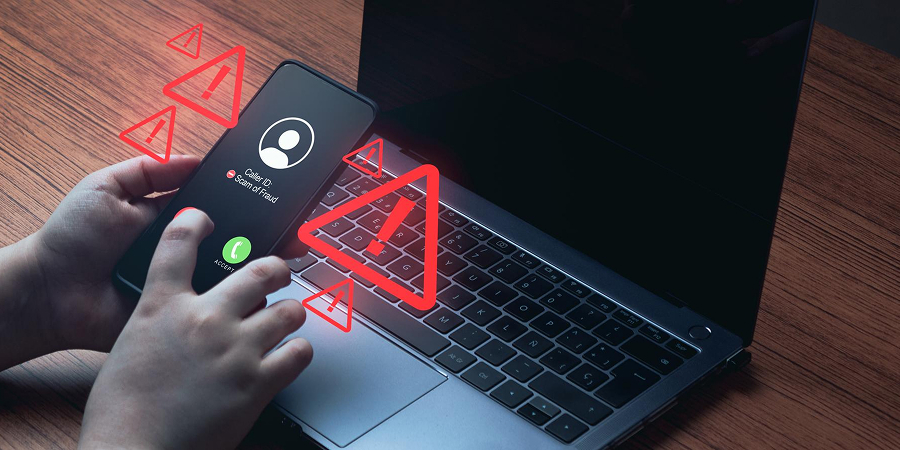
Smishing (SMS Phishing)
Smishing is a type of fraudulent text messaging that aims to fool recipients into clicking on malicious links or providing sensitive information. It regularly spoofs delivery services, banks, or government agencies to build excitement and credibility.
How it works
- You get an email saying that it is a bank or some government agency.
- It entails a request or deduction of personal data.
- The connection can be exploited to install malware or run counterfeit login sites.
Always beware of clicking on links in messages that are not familiar, and always consult authorized sources first before subjecting your own mobile device to smishing attacks.
Vishing (Voice Phishing)
Vishing is the use of voice-over-IP to manipulate the targets into revealing sensitive data over the voice phone. They tend to use spoofed identities and compelling scripts to adopt alternate identities of banks or official governmental agencies.
How it works
- The caller impersonates a bank or tech support member or a government building.
- They forcibly get you to share personal information like OTPs or passwords.
- Some people spoof their numbers and appear authentic.
Why it works
Personal communication creates an element of trust, which makes it difficult to commit lies.
Clone Phishing
Clone phishing involves copying genuine emails that are already in the possession of the receiver and replacing the non-hazardous links or attachments with the malicious ones. This will render the message as part of the norm, and there are high chances of users playing around with the message.
How it works
- The text of the message of the first email is literally copied.
- The cloned version replaces legitimate links or attachments with malicious ones.
- It exerts itself in re-sending or a modified one.
Result
The victims will be more relaxed about being there, and they will have a higher possibility of trusting it.
Pharming
Pharming is a trick of redirecting people without their knowledge to a rogue site by altering DNS settings or installing malware. This allows the attackers to steer clear of sensitive information even when users type the correct URL directly into their browser.
How it works
- Malware redirects traffic by manipulating DNS.
- The fake website is similar to the original.
- The user unintentionally types usernames and passwords.
Key concern
Even cautious users may get hooked, as there is no suspect linkage.
Social Media Phishing
Phishing is done via social media, such as LinkedIn or Instagram. They falsify accounts, messages, or promises to lure users to click on lethal links or supply personal and professional data.
How it works
- Fraudulent profiles are the simulation of others/brands.
- Messages may contain malicious links or fake job offers.
- Attackers exploit trust and curiosity.
To avoid phishing attacks on social media, it is advisable to check the profiles, be cautious of unknown links, and not to post any personal and professional information on the Internet.
Angler Phishing (Customer Support Scams)
Angler phishing is aimed at online users who are interested in receiving support with referencing official customer care accounts. It redirects them to fraudulent assistance platforms through which attackers get access to login details or credit cards.
How it works
- Those who attack impersonate customer care accounts on social media.
- They do not give out complaints or questions.
- The victims are referred to phony support systems where they lose their credentials.
Users can stay protected against a deceptive customer support phishing scam on the Internet by relying solely on official support channels and neglecting unsolicited responses.
Final Thoughts
Phishing now is not a simple scam, but a clever, flexible, and more and more automated, AI-driven technique. Knowing the various types of phishing attacks is an invaluable tool that helps you recognize threats before they strike.
With Jortty, your trusted tech concierge, you gain proactive protection, expert guidance, and real-time support to navigate today’s complex cybersecurity landscape with confidence. Contact us today to secure your systems, protect your data, and gain complete peace of mind in an increasingly risky digital world!
Frequently Asked Questions
How do phishing attackers get my personal information?
Hackers gather information with breaches, scraping data from social media, public records, and data broker databases online.
Can phishing attacks happen without clicking any links?
Yes, threats, such as pharming or spoofing, redirect the user or steal data without the user having to interact with the link.
Are phishing attacks increasing with new technologies like AI?
Yes, AI is helping to scam people more convincingly and quickly through automation, deepfakes, and scale personalization techniques. However, the evolution of scam detection tools helps to avoid scams online.